I recently attended the first day of IP Expo 2014, mostly because of the co-hosted Cyber security event that was happening concurrently, but also to see Tim Berners-Lee talk. And to browse the stalls a bit.
The last time I was anywhere near London’s Excel centre, where the event takes place, I was blockading the DSEi arms fair, so it was a little strange to be rubbing shoulders with the suits inside the venue. And there were a lot of suits.
There were also a lot of vendors too. Mostly repeating the words business
and cloud
to said suits ad-infinitum. I did, however, collect an awful lot of pens and a plastic axe so the presence of the vendors was not without benefit.
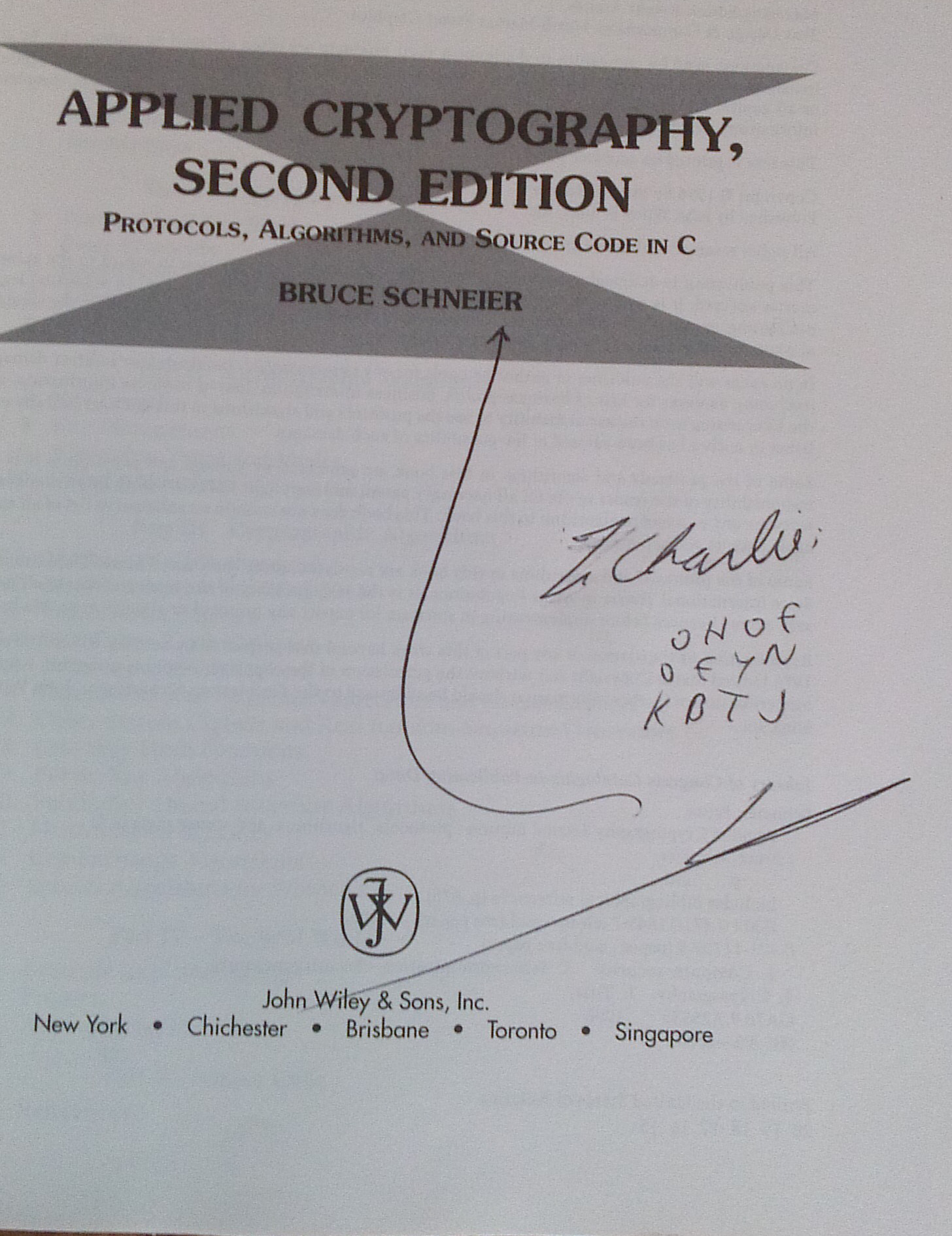
The absolute highlight of the day for me was getting my copy of Applied Cryptography signed by Bruce Schneier. As you can see he even did a bit of crypto in his autograph.
Can’t figure out what OHOE OEYN KBTJ
means? I have ROT13ed a spoiler, you can unROT13 it using my un-ROT13 tool if you like.
Spoiler Vg fnlf 'rawbl gur obbx'. Ernq vg sebz gur gbc evtug, ol pbyhza sebz evtug gb yrsg.
Here are some highlights of the talks I attended from the notes I took.
Tim Berners-Lee
Tim was doing his mad professor routine, struggling with some very boomy sound and a lot of background noise. His talk was about the web in 2050 and he had a few interesting thoughts:
Tim’s boss thought his original WWW memo wasvague but exciting
- He talked a lot about the broken privacy model that leaves out data producers like you and I from a nuanced discussion of how our data might be used.
- We should be able to know when someone accesses our data and why in Tim’s opinion.
- He does not agree with the
privacy is dead, get over it
view. - His boss wrote on his WWW memo that the project seemed
vague but exciting
and these properties are what made the web great. - We need a better informed democratic debate about the web.
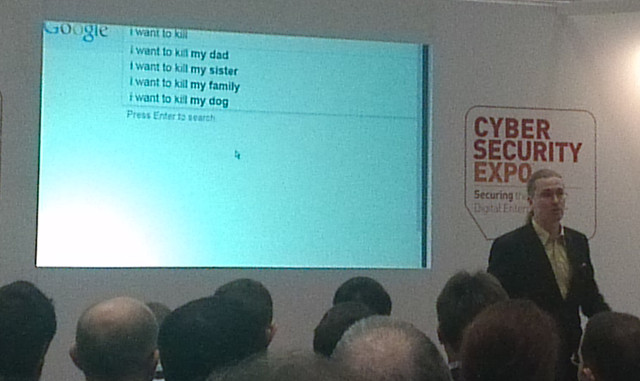
Mikko Hyponnen
Mikko gave a great and hard-hitting presentation entitled Living In a Surveillance State that drew together a number of privacy related themes.
- F-Secure recently set up a wifi access point with a licence requiring in the terms and conditions that the user to sign over their firstborn child in order to use the wifi. Needless to say everyone agreed to the T&Cs!
- There is a spoof app originating on the Chinese mainland and containing a trojan being circulated amongst Hong Koong protestors at the moment.
- Google, Facebook and the rest are just as involved in the surveillance business.
There are no free search engines
. - Volunteering your data to Google is sharing it with the NSA.
- George Orwell was an optimist. He only imagined 2 way TVs. The reality is much worse.
Bruce Schneier
Bruce talked about incident response, his talk included some interesting information from economics and psychology.
Current trends
- We are losing control over our data and our infrastructure. The cloud means that our data is not on our computers so we can’t affect its security.
- Attacks are getting more sophisticated. We are seeing sophisticated weapons in unsophisticated hands
- Cyber crime has matured as an industry
- There will be more state involvement and regulation online in the future.
- The cyber-weapons arms race continues
Economics
- Metcalfe’s law means that big players get bigger where network effects are critical.
- Fixed costs and marginal costs are important to understand in IT security. Attacks are valuable when they allow attacker to take advantage of near-zero marginal cost.
- Switching costs are high in technology industry.
The higher the switching costs the more you can piss off your customers before they switch
- Tech security is a lemons market — bad products do well in it. Eg. Firewalls in the 90s, IDSes in the 2000s.
Psychology
- Prospect theory is at play in security industry.
Security is people, a process, and a product
but the ratios change. Incident response can’t be automated, so the people to tech ratio goes up.- Scaling is hard (in incident response). Tech has to serve rather than replace people.
- The OODA loop is critical in response.